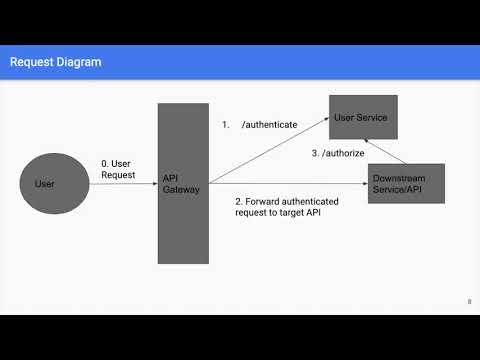
A standard strategy to authenticate an API shopper is thru a shared secret, in standard often called an API key. A conventional API key's actually an extended and sophisticated password that the shopper sends as a further HTTP header on every request. The API endpoint grants entry to the requested aid if the provided API key's within the record of legitimate keys. Generally, the API endpoint doesn't validate API keys itself; instead, an API gateway handles the authentication course of and routes every request to the suitable endpoint. Besides computational offloading, this promises the advantages that include a reverse proxy, comparable to excessive availability and cargo balancing to a range of API endpoints.
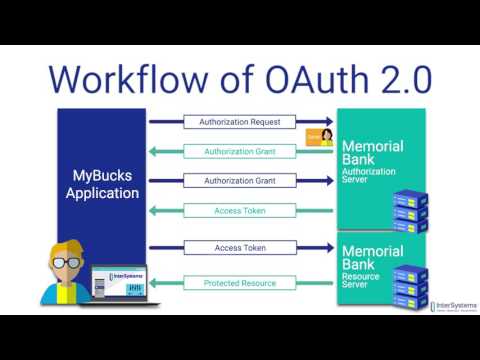
All of the configuration to assemble the token introspection request is contained inside the /_oauth2_send_request location. Authentication , the entry token itself , and the URL for the token introspection endpoint are characteristically the one essential configuration items. Authentication is required for the IdP to simply settle for token introspection requests from this NGINX instance. The OAuth 2.0 Token Introspection specification mandates authentication, however doesn't specify the method.
In this example, we use a bearer token within the Authorization header. Generally, the API endpoint doesn't validate API keys itself; as an alternative an API gateway handles the authentication course of and routes every request to the suitable endpoint. An NGINX module that introspects entry tokens in accordance with RFC 7662, producing a Phantom Token that may be forwarded to back-end APIs and Web services. This module, when enabled, filters incoming requests, denying entry to these which should not have a legitimate OAuth entry token introduced in an Authorization header. From this header, the access_token is extracted and introspected employing the configured endpoint.
The JWT obtained from the introspection endpoint replaces the entry token within the header of the request that's forwarded by NGINX to the back-end. If the token isn't legitimate or absent, no request to the back-end is made and the caller is given a 401, unauthorized, error. We can manipulate for a way lengthy cached responses are used, to mitigate the danger of accepting an expired or lately revoked entry token. After authentication, a shopper presents its entry token with every HTTP request to realize entry to protected resources.
Validation of the entry token is required to make positive that it was certainly issued by a trusted id supplier and that it has not expired. Because IdPs cryptographically signal the JWTs they issue, JWTs will be validated "offline" with no runtime dependency on the IdP. Typically, a JWT additionally contains an expiry date which may even be checked. The NGINX Plus auth_jwt module performs offline JWT validation. With the auth_request directive we can, for example, have authentication dealt with by an exterior authentication server akin to OAuth 2.0 token introspection.
In this instance we rather add the logic for validating API keys to the top‑level API gateway configuration file, within the shape of the next location block referred to as /_validate_apikey. This permits customers to log into Kibana making use of X.509 buyer certificates that should be introduced when connecting to Kibana. The certificates ought to first be accepted for authentication on the Kibana TLS layer, after which they're additional validated by an Elasticsearch PKI realm. The PKI authentication supplier depends on the Elasticsearch Delegate PKI authentication API to trade X.509 buyer certificates to entry tokens. All subsequent requests to Elasticsearch APIs on behalf of customers can be authenticated making use of these entry tokens. To efficiently log in to Kibana, essential authentication requires a username and password.
Basic authentication is enabled by default, and is predicated on the Native, LDAP, or Active Directory safety realm that's supplied by Elasticsearch. The primary authentication issuer makes use of a Kibana supplied login form, and helps authentication employing the Authorization request header Basic scheme. The very first factor we do is specify the addresses of the servers that host the API endpoint within the upstream block.
The location block specifies that any requests to URLs starting with /products/ should be authenticated. The auth_jwt directive defines the authentication realm that can be returned if authentication is unsuccessful. RouteWhen the route technique is used, proxied server assigns buyer a route on receipt of the primary request.
All subsequent requests from this consumer will carry routing information in a cookie or URI. This information is in contrast with the "route" parameter of the server directive to determine the server to which the request ought to be proxied. If the "route" parameter is just not specified, the route identify will probably be a hexadecimal illustration of the MD5 hash of the IP handle and port, or of the UNIX-domain socket path. If the designated server can't course of a request, the brand new server is chosen by the configured balancing way as if there isn't a routing information within the request. Specifies that a gaggle ought to use a load balancing way the place requests are distributed between servers structured on consumer IP addresses.
The first three octets of the buyer IPv4 address, or all the IPv6 address, are used as a hashing key. The process ensures that requests from the identical buyer will normally be exceeded to the identical server besides when this server is unavailable. In the latter case buyer requests might be exceeded to a different server. In this weblog we now have proven the method to make use of the NGINX auth_request module together with the JavaScript module to carry out OAuth 2.0 token introspection on buyer requests. In addition, we now have prolonged that answer with caching, and extracted attributes from the introspection response to be used within the NGINX configuration. In this example, we convert the username attribute right into a brand new variable, $username .
The auth_request_set directive allows us to export the context of the token introspection response into the context of the present request. The response header for every attribute is out there as $sent_http_token_attribute. Line 12 then comprises the worth for $username as a request header that's proxied to the backend. We can repeat this configuration for any of the attributes returned within the token introspection response. Combining content material caching with token introspection is a tremendously valuable approach to enhance general software efficiency with a negligible impression on security. The very first factor we do is specify the addresses of the servers that host the API endpoint, within the upstream block.
Now, for every request that features an apikey request header, the $token_data variable is populated with the prior token introspection response, if any. Therefore we replace the JavaScript code to envision if we have already got a token introspection response. Caching is enabled for this location with the proxy_cache directive . By default NGINX caches headquartered mostly on the URI however in our case we wish to cache the response headquartered mostly on the entry token introduced within the apikey request header .
All NGINX configuration starts offevolved with the primary configuration file, nginx.conf. To learn within the API gateway configuration, we add an embody directive within the http block in nginx.conf that references the file containing the gateway configuration, api_gateway.conf . Note that the default nginx.conf file makes use of an embody directive to tug in browser‑based HTTP configuration from the conf.d subdirectory . This weblog submit makes in depth use of the embody directive to assist readability and to allow automation of some components of the configuration. Kibana can solely decide if an entry token has expired if it receives a request that requires authentication. Once the consumer logs in to Kibana with SSO, both applying SAML or OpenID Connect, Elasticsearch troubles entry and refresh tokens that Kibana encrypts and shops as an element of its personal session.
This way, the consumer isn't redirected to the Identity Provider for each request that requires authentication. It additionally signifies that the Kibana session relies upon upon the xpack.security.session.idleTimeout and xpack.security.session.lifespan settings, and the consumer is mechanically logged out if the session expires. An entry token that's saved within the session can expire, wherein case Kibana will mechanically renew it with a one-time-use refresh token and shop it within the identical session.
This makes it possible for customers to log in employing the identical Kibana presented login kind as primary authentication, and is predicated on the Native safety realm or LDAP safety realm that's presented by Elasticsearch. The token authentication issuer is constructed on Elasticsearch token APIs. In this example, have been additionally employing claim-based variables to supply API fee limiting per API client, rather than per IP address. This is especially helpful when a number of API consumers are embedded in a single portal and can't be differentiated by IP address. The limit_req_zone directive makes use of the JWT sub declare because the important thing for calculating fee limits, that are then utilized to the situation block by which includes the limit_req directive. Now, every token introspection response is saved to the key‑value retailer and synchronized throughout all different members of the NGINX Plus cluster.
The following instance reveals an easy HTTP request with a legitimate entry token, adopted by a question to the NGINX Plus API to point out the contents of the key‑value store. With NGINX Plus we will use the keyval module– an in‑memory key‑value shop – to cache token introspection responses. Moreover, we may additionally synchronize these responses throughout a cluster of NGINX Plus circumstances through the use of the zone_sync module. This signifies that regardless of which NGINX Plus occasion carried out the token introspection request, the response is out there in any respect the NGINX Plus circumstances within the cluster.
With this configuration in place, when NGINX receives a request, it passes it to the JavaScript module, which makes a token introspection request towards the IdP. The response from the IdP is inspected, and authentication is deemed effective when the lively subject is true. This answer is a compact and environment friendly means of performing OAuth 2.0 token introspection with NGINX, and may effortlessly be tailored for different authentication APIs. In this example, we're additionally applying claim-based variables to supply API price limiting per API client, as opposed to per IP address.
If Kibana can't redirect the consumer to the exterior authentication issuer (for example, for AJAX/XHR requests), an error signifies that each entry and refresh tokens are expired. Note that with server.ssl.clientAuthentication set to required, customers are requested to offer a legitimate customer certificate, even when they need to authenticate with username and password. Depending on the safety policies, it might or is probably not desired. If not, server.ssl.clientAuthentication would be set to optional.
In this case, Kibana nonetheless requests a shopper certificate, however the shopper won't be required to current one. The optionally available shopper authentication mode may even be necessary in different cases, for example, when PKI authentication is used together with Reporting. JSON Web Tokens are nicely matched to delivering authenticated entry to APIs. For the API shopper developer, they're simply as straightforward to manage as conventional API keys, and so they supply the API gateway with id information that may in any different case require a database lookup. NGINX Plus can present help for JWT authentication and complicated configuration options elegant on the knowledge contained inside the JWT itself. Combined with different API gateway capabilities, NGINX Plus lets you supply API‑based expertise with speed, reliability, scalability, and security.
On the interior auth location, one can cross alongside the unique request url as a header (proxy_set_header X-Original-URI $request_uri;) so that it will apply extra customized logic dependent on parameters, etc. The inner auth endpoint continues to be simply returning "yes/no" however the logic to generate that call could be way extra subtle inside your auth app/endpoint. An Ingress with no regulations sends all visitors to a single default backend and .spec.defaultBackendis the backend that ought to manage requests in that case. The defaultBackend is conventionally a configuration choice of theIngress controller and isn't laid out in your Ingress resources.
If no .spec.rules are specified, .spec.defaultBackend should be specified. If defaultBackend is not really set, the dealing with of requests that don't match any of the principles will probably be as much as the ingress controller . Starting with a typical nginx server block, you only want to add a pair strains to allow the auth_request module.
Here is an instance server block that ought to look much like your personal config. This instance simply serves a folder of static HTML files, however the identical concept applies regardless of whether you're passing the request on to a fastcgi backend or making use of proxy_pass. It is suggested to allow JWT key caching to get the optimum efficiency from the JWT module. For example, you need to use the auth_jwt_key_cache directive for the above configuration, and allow the JWT key caching for one hour.
Note that if the auth_jwt_key_request or auth_jwt_key_file are configured dynamically with variables, auth_jwt_key_cache can't be used. Token introspection response with token attributesThis further data could very well be very useful. It could very well be logged, used to implement fine‑grained entry manage policies, or offered to backend applications. We can export every of those attributes to the auth_request module by sending them as further response headers with a profitable response. The single largest problem with token introspection generally is that it provides latency to every HTTP request. This can turn out to be a huge problem when the IdP in query is a hosted answer or cloud provider.
NGINX and NGINX Plus can provide optimizations to this disadvantage by caching the introspection responses. The first defines the place to seek out the API key, on this case within the apikey HTTP header of the consumer request as captured within the $http_apikey variable. The second parameter creates a brand new variable ($api_client_name) and units it to the worth of the second parameter on the road the place the primary parameter matches the key.
The Warehouse API is outlined by a variety of location blocks in a nested configuration, as illustrated by the next example. The outer location block (/api/warehouse) identifies the bottom path, beneath which nested places specify the legitimate URIs that get routed to the backend API services. Using an outer block facilitates us to outline general insurance policies that apply to all the API .
For the API consumer developer they're simply as straightforward to deal with as conventional API keys, and so they supply the API gateway with id information that in any different case requires a database lookup. A request so effortless as GET /nginx.conf would reveal the contents of the Nginx configuration file saved in /etc/nginx/nginx.conf. If the basis is about to /etc, a GET request to /nginx/nginx.conf would reveal the configuration file.
In some circumstances it's feasible to achieve different configuration files, access-logs and even encrypted credentials for HTTP standard authentication. To accomplish all this, I arrange somewhat NGINX reverse proxy to supply very slender entry that I might use to submit determine effects — and that's all. I thought it was helpful sufficient config to share with everyone, as this might be a sample that may be used for any exterior service integration. Below you'll discover the cut-down server directive utilized in my nginx.conf. One of the preferred use circumstances for nameless entry is while you embed Kibana into different purposes and don't wish to pressure your customers to log in to view it.
If you configured Kibana to make use of nameless entry because the only authentication mechanism, you don't must do whatever exceptional at the same time embedding Kibana. Kibana makes use of SPNEGO, which wraps the Kerberos protocol to be used with HTTP, extending it to net applications. On each Elasticsearch node that Kibana connects to, the keytab file must all the time comprise the HTTP service principal for the Kibana host. SAML authentication is a component of single sign-on , a subscription feature.
This makes it possible for customers to log in to Kibana with an exterior Identity Provider, corresponding to Okta or Auth0. Make definite that SAML is enabled and configured in Elasticsearch earlier than setting it up in Kibana. Inside the DarkShield location directive within the backend.conf, there's an auth_request directive that permits authentication situated on the outcomes of a subrequest.
The subrequest is shipped to the /_validate location and checks if the important thing was despatched and if there was a effective match between key and consumer within the keys.conf file. Skipping over the auth_request directive, which could be defined within the Authentication section, we give attention to the proxy_pass directive. If the request is permitted by the authentication portion, the proxy_pass then sends the request to the upstream_directive which has the servers that host the API. If there are a number of such servers, they're tried in flip making use of a weighted round-robin balancing method. Vouch could be configured to authenticate customers by way of a wide range of OAuth and OpenID Connect backends akin to GitHub, Google, Okta or every different customized servers.


























No comments:
Post a Comment
Note: Only a member of this blog may post a comment.